
Automate Cybersecurity Defense
Gain persistent cyber asset visibility, harden your attack surface, align with policy standards, and focus SecOps on high value tasks. Start 30-day Free TrialCyber Asset Attack Surface Management (CAASM) Simplified



Benefits of Visore Security Platform
Comprehensive Asset Visibility
The shift to the cloud is enabling organizations to manage costs and accelerate business. However, the visibility and management of assets across a hybrid environment has become complex and time consuming.
Solution:
Quickly identify potential threats to your organization’s critical assets before they are exploited.

Interoperability of Tools
The average number of security and IT tools in organizations continue to increase while the level of complexity and time it takes to analyze data from these tools has gone up.
Solution:
Don’t get pinned down by closed end systems, swap out tools in your environment at anytime without disrupting your team’s productivity.
Better Decision Making
Security operations have become complex with overlapping data and alerts that cause fatigue and burnout.
Solution:
Improve your overall risk profile with clear and actionable insight that drives automation in your security operations.

Improve Efficiency of Security Operations
The rise of hybrid work environment along with an exponential increase in data and tools complexity has led to manual and error prone processes within SecOps.
Solution:
Benchmark operations and prioritizes actions that lead to the highest value towards reducing risk.
Improve productivity as security teams can now focus on implementation versus endless analysis.
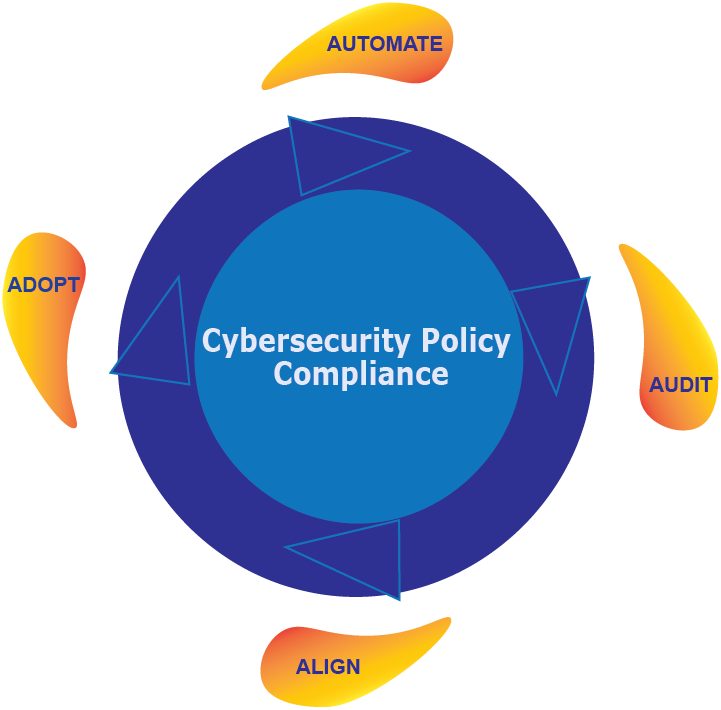
Faster Policy Compliance
Compliance with industry standards is a continuous never-ending cycle. More organizations are required to meet compliance standards to do business than ever before.
Solution:
Automate compliance processes to save time and dramatically reduce the risk and high costs associated with non-compliance.
Create policy at multiple levels and asset classes to allow flexibility in business operations.
Visore Security Platform Enables Automation
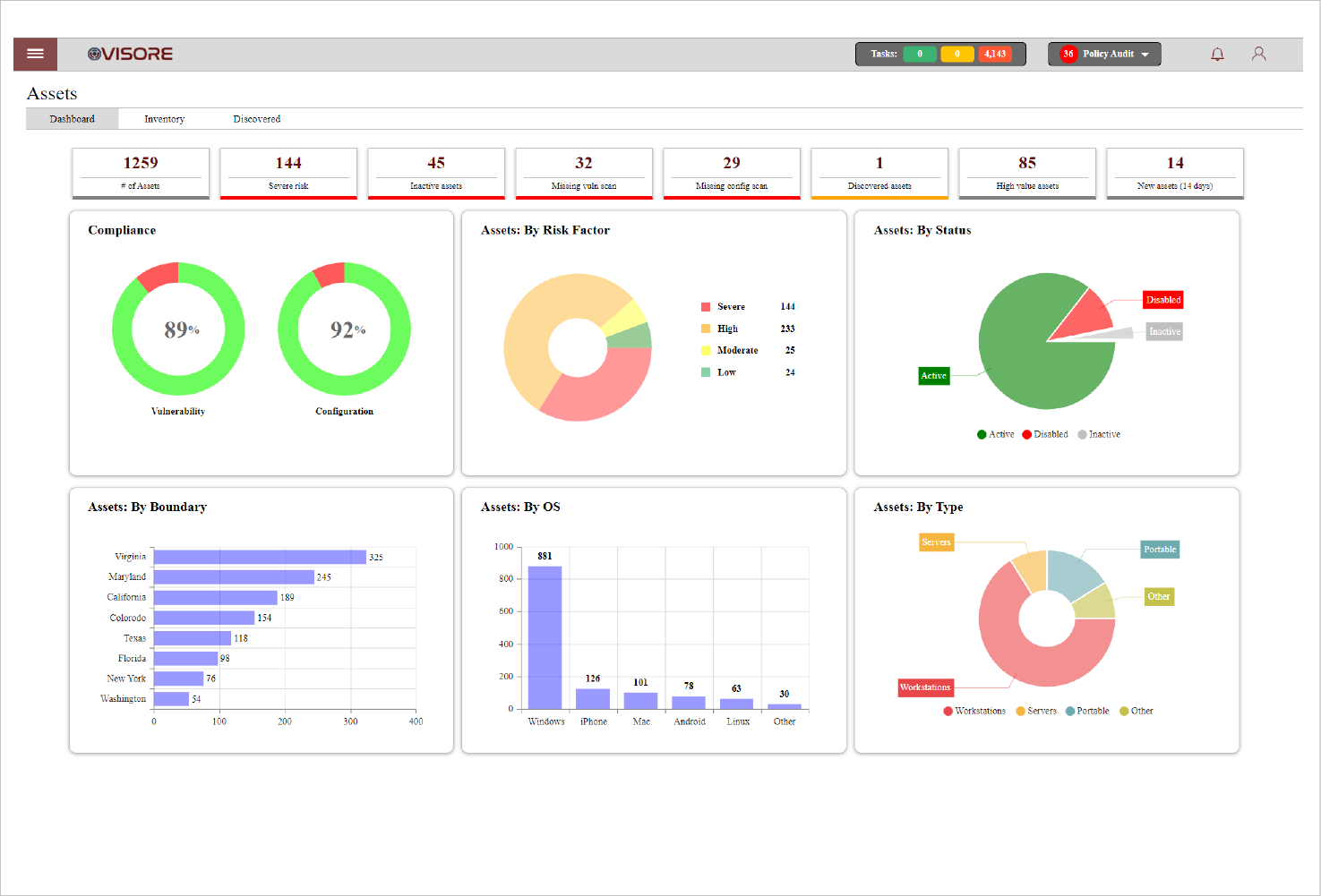
Asset Visibility
Gain comprehensive asset inventory and quickly identify gaps in coverage using out of the box integrations with tools in your existing environment.
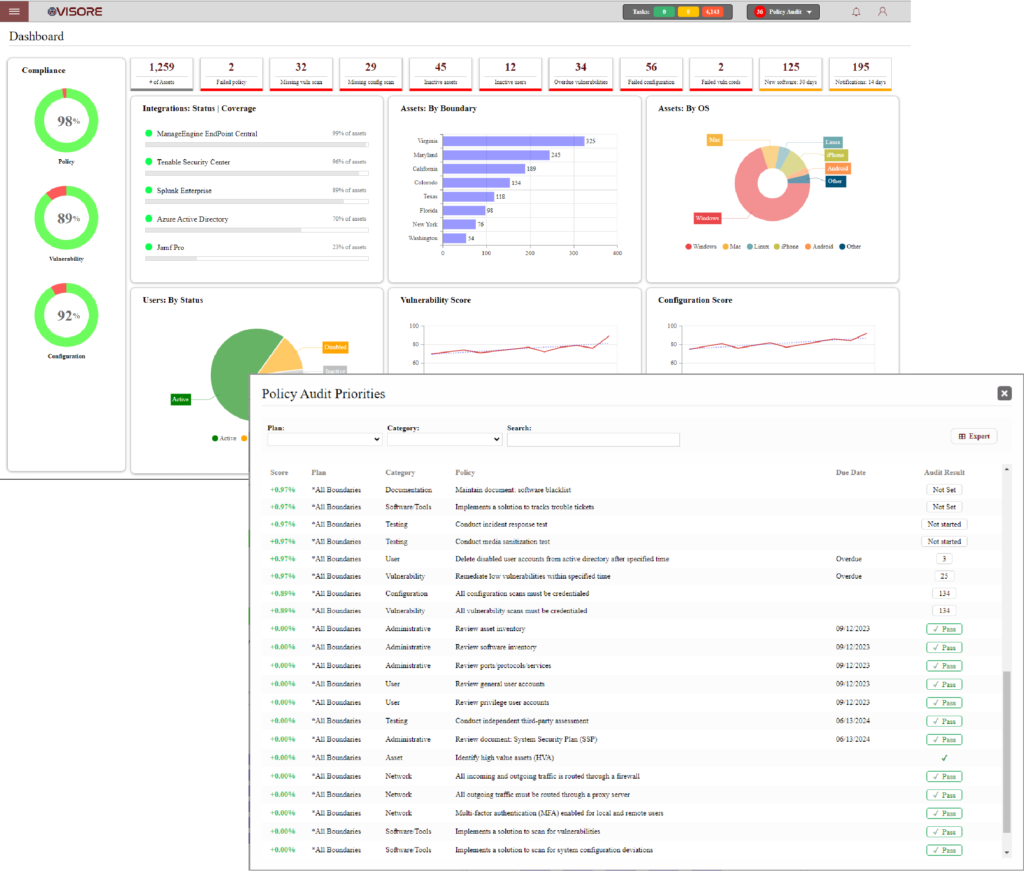
Security Orchestration
Automatic task creation, assignment, reporting, and notifications to track your progress to policy compliance.
Policy Compliance
Align security operations to ISO or NIST standard with over 50 policies out of the box that help accelerate adoption.
Vulnerability Management
Track progress, compliance, and efficacy over time to help you prioritize vulnerabilities for high value assets (HVA).
Events & Alerts
Consolidate and reduce alerts by integrating with your SIEM, EDR and other tools to help you prioritize high value actions.
System Configuration
Simplify thousands of compliance checks into a concise summary while tracking the efficacy via configuration risk score over time.
Case Studies
Don’t just take our word for it. We have been recognized by Clutch as a top 100 security software provider thanks to our amazing customers and our commitment to their success. Here are a few examples of what our customers can achieve after adopting Visore Security Management Platform:
SMB
Doing more with less
Small to medium sized companies compete for scarce resources as they grow.
Results Achieved: Visore Security Platform helped a private sector organization to manage the end-to-end security operations, including compliance with NIST 800-53, with only two resources paving the way for winning federal government contracts.
Enterprise
Prioritize what is important
The number of IT and security tools needed to manage cybersecurity has increased.
Results Achieved: Visore Security Platform helped a multi-national organization to connect all their IT and security data into a single platform reducing their remediation time by 31% while eliminating redundant tasks brought on by duplicate alerts.
Public Sector
Managing asset visibility
Identify asset inventory and functional purpose for each asset.
Results Achieved: Visore Security Platform helped a public sector organization index their entire network which saw a 60% increase in their known assets inventory and significant improvement to their security posture.
Customer Support

Product Training:
We understand our customers have limited time for training. Most users will be up and running in less than a day with our virtual training session.

Implementation:
Minimal installation and configuration time. Visore is designed with quick-start in mind getting you up and running in no time.
Integration:
We integrate with all leading security tools and as our brand promise, we will take care of the integration if we don’t already have it built.
Ongoing Support:
Our live phone support and quick reply email support helps make sure you’re always getting value from Visore.


